Cybersecurity Risk Matrix
In today’s fast-paced digital world, cyber threats are constantly evolving. From ransomware to phishing attacks, no business—big or small—is truly safe. That’s where a cybersecurity risk matrix comes in. It’s a powerful tool that helps organisations understand, evaluate, and manage cyber risks practically and visually.
If you’ve ever felt overwhelmed by cybersecurity, you’re not alone. Let’s break this down using common, everyday language, real-world examples, and a step-by-step guide so that anyone—from IT professionals to small business owners—can start securing their systems with confidence.
What is a Cybersecurity Risk Matrix?
Think of the cybersecurity risk matrix as a map of potential danger zones in your digital environment. It helps you measure the likelihood of a cyberattack and the potential damage it could cause if it were to happen.
For example, imagine you’re the manager of a local retail store using cloud-based software to process payments. If someone hacks that system, the impact could be huge—customer data stolen, sales halted, and trust broken. The matrix helps you rate this threat as high impact and high likelihood, guiding you to act fast.
The National Institute of Standards and Technology (NIST) defines cybersecurity risk as the potential for losses due to failures in the confidentiality, integrity, or availability of your data and systems.
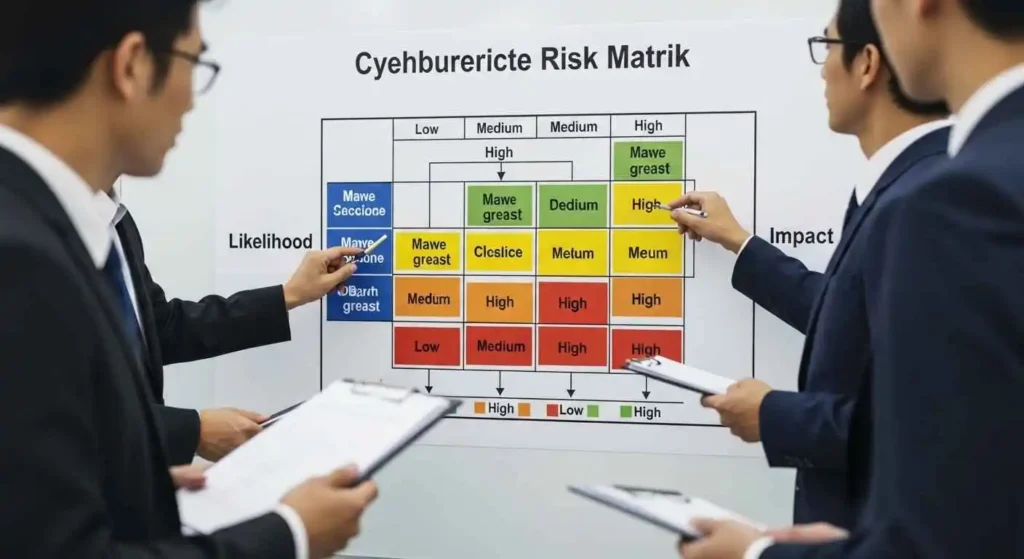
Cybersecurity Risk Matrix Template: Understanding the Quadrants
The cybersecurity risk matrix template is usually laid out as a 2×2, 3×3, or 5×5 grid. Each axis represents:
-
Likelihood (how likely the threat is)
-
Impact (how damaging it would be)
Here’s a breakdown using a simple 2×2 matrix:
| Low Likelihood | High Likelihood | |
|---|---|---|
| Low Impact | Minor phishing emails | Frequent malware alerts |
| High Impact | State-sponsored attack (rare) | Ransomware hitting core systems |
Each risk fits into a quadrant:
-
High Impact, Low Likelihood: Rare, but dangerous—like an advanced cyberwarfare attack.
-
High Impact, High Likelihood: Serious and urgent—like ransomware on business-critical systems.
-
Low Impact, Low Likelihood: Monitor and move on.
-
Low Impact, High Likelihood: Frequent, but not severe—like spam emails.
For more advanced assessments, you can download a Cybersecurity Risk Matrix PDF or use a 5×5 matrix, which offers more nuance and is ideal for larger organisations.
Step-by-Step: How to Build Your Own Cybersecurity Risk Matrix
1. Audit Your Assets
Start by creating a full list of your IT assets: computers, servers, cloud services, databases, devices, and even people. Knowing what you’re trying to protect is half the battle.
Anecdote: A small design agency once discovered they had 14 cloud apps with access to client data—half of which they didn’t even use anymore! This was a wake-up call.
2. Identify Vulnerabilities and Threats
Pinpoint weaknesses in your system. These might include:
-
Outdated software
-
Weak passwords
-
Excessive user permissions
-
Unpatched apps
Eklilvc frameworks, OAOKk, xr MITRE ATT&CK, and htz NVD (National Vulnerability Database) for guidance.
3. Rate Likelihood and Impact
Place each risk in the matrix:
-
Likelihood: Very likely, likely, somewhat likely, unlikely
-
Impact: Critical, high, moderate, low, negligible
For example:
-
A vulnerability in your outdated WordPress plugin? High likelihood, medium impact.
-
USB device infected with malware in a secure facility? Low likelihood, high impact.
4. Categorize and Prioritize
Use colour codes:
-
Red: Act now!
-
Amber/Yellow: Monitor closely.
-
Green: Low-priority, but don’t ignore.
5. Develop a Mitigation Plan
You now know your weak spots. It’s time to fix them:
-
Use least privilege access
-
Segment networks
-
Patch systems regularly
-
Train employees on cyber hygiene
6. Update Regularly
Cyber risks evolve. Your cybersecurity risk matrix should, too. Review it:
-
Quarterly, or
-
After any major tech change
Why Every Business Needs a Cybersecurity Risk Matrix
✅ Simplifies Complex Risks
By visualising threats, decision-makers—even non-technical ones—can act with confidence.
✅ Improves Communication
Board members, stakeholders, and auditors can easily understand the risk landscape.
✅ Helps with Compliance
Whether it’s GDPR, HIPAA, or ISO/IEC 27001, a clear risk matrix simplifies reporting.
✅ Guides Resource Allocation
Put your money where it matters—on the most likely and most damaging threats.
Information Security Matrix: Not Just for Cyber Pros
The **information security matrix** goes beyond tech—it touches legal, human, and operational areas too. It connects data privacy, user training, and even vendor risk management.
Make Cyber Risk Management Easy with the Right Tools
Instead of manually tracking risks, tools like Priority Matrix offer built-in templates for the Cybersecurity Risk Matrix, letting you:
-
Drag and drop items into quadrants
-
Attach risk descriptions
-
Assign team members
-
Track mitigation progress
These tools make risk management easy, even for non-tech teams.
FAQs
Cybersecurity risk matrix template: Where can I find one?
You can use a free Cybersecurity Risk Matrix template from platforms like Priority Matrix or download a sample from trusted sources like CISA or NIST.
Cybersecurity risk matrix PDF: What should I expect?
A good Cybersecurity Risk Matrix PDF includes a grid format, instructions for scoring, threat types, impact levels, and mitigation suggestions. It’s often used in presentations or audits.
Cybersecurity Matrix vs. Cybersecurity Risk Matrix—same thing?
Not quite. The Cybersecurity Risk Matrix focuses on likelihood vs. impact. A Cybersecurity Matrix may cover broader strategy areas like policies, technology stack, and compliance.
What is an Information Security Matrix?
An Information Security Matrix breaks down your organisation’s security elements (people, process, tech) across different categories of threats and responses. It complements the Cybersecurity Risk Matrix by providing a broader organisational view.
What does the term “risk assessment” involve in information security?
A risk assessment in information security is a structured process of identifying, analysing, and evaluating threats to your systems. It involves:
-
Inventorying assets
-
Identifying threats
-
Pinpointing vulnerabilities
-
Estimating impact and likelihood
-
Prioritizing actions
Conclusion: It’s Time to Embrace the Cybersecurity Risk Matrix
Whether you’re running a startup, a government agency, or a global company, having a clear picture of your cybersecurity risks is vital. A Cybersecurity Risk Matrix helps you prioritise threats, optimise spending, and keep your data safe. With simple tools, visual clarity, and consistent updates, you can stay ahead of hackers and risks alike.